Supply Chain Attacks On The Menu In 2022
- Admin
- Mar 15, 2022
- 2 min read
Published: March 15, 2022 on our newsletter Security Fraud News & Alerts Newsletter.

As has been established, repeatedly, the cybersecurity threat landscape is ever evolving. There are no holidays or breaks for threat actors. In fact, they are especially good at their jobs and make it as easy on themselves as possible. They find a vulnerability and they pounce on it like a lion on a water buffalo. Unfortunately, businesses sometimes make it even easier on them by not adequately protecting themselves. Unfortunately, the supply chain is slowly approaching water buffalo status for the hungry cybercriminals.
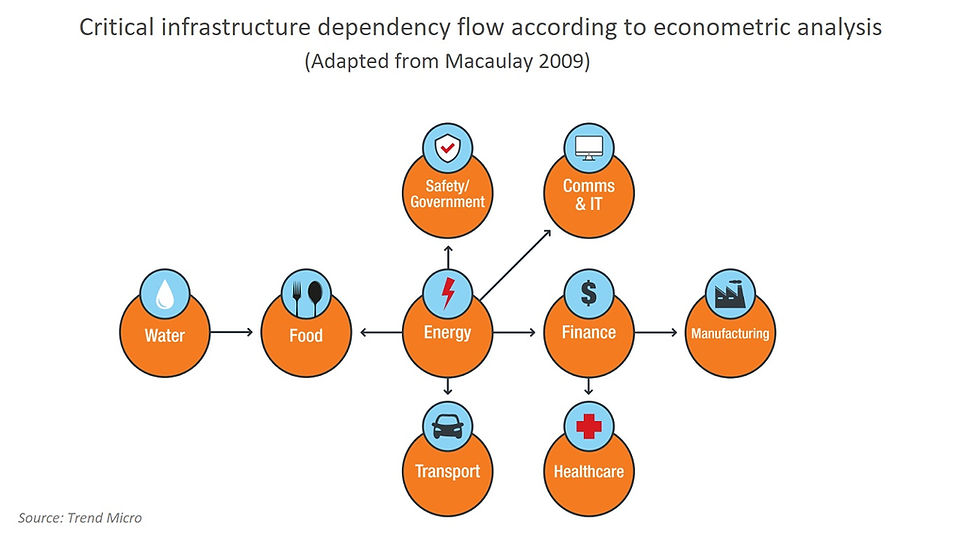
As we’ve recently seen, critical infrastructure is in that bullseye. While the energy sector is a primary target of critical infrastructure cyberattacks, it is certainly not alone. Transportation, public sector services, telecommunications, and manufacturing industries are also on the menu throughout 2022.
Research from Trend Micro reported that 54% of the 500 critical infrastructure suppliers in the U.S. that were surveyed, reported attempts of someone trying to control systems. Forty percent (40%) had experienced attempts to shut down systems.
Why is it so easy to attack the supply chain? Often, it’s because they have smaller budgets for cybersecurity protection. It’s also because they frequently use legacy software that is no longer supported by developers, leaving it more vulnerable to attacks. Adding fuel to the fire, these are industries where emails get sent around at the speed of a cheetah, making social engineering, specifically phishing, rather lucrative. After all, there is a lot of valuable data in these areas.
But it’s not just critical infrastructure that needs to stay on top of this. All organizations, regardless of size, location, or industry are vulnerable.

How to keep out of the food chain
Avoid the phishing lures. All users should watch for links and attachments that are at all suspect. If there is any uncertainty, don’t bite.
Be conservative about what is on social media, including business networking sites such as LinkedIn. Those are a treasure-trove of information for would-be attackers. The more that’s posted there, the more material any attacker has to work with and they do look and they do note it. This not only applies to the individuals, but also to organizations who have a presence on these sites.
Make sure all systems are patched and kept updated at all times. Those legacy systems? They’re an attack waiting to happen. Try to keep them as secure as possible and upgrade when possible, but certainly when a product is no longer supported.
Implement a cybersecurity training program that is continuous. Don’t just do it annually and consider it done. Cyber threats change quickly and throughout the year. There are no seasons of cybersecurity attacks.
Keep up to date: Sign up for our Fraud alerts and Updates newsletter
Want to schedule a conversation? Please email us at advisor@nadicent.com



Comments