U.S. Government Warns of Malware Holding Healthcare Industry Hostage
- Admin
- Mar 5, 2021
- 2 min read
Published: November 18, 2020 on our newsletter Security Fraud News & Alerts Newsletter.

The U.S. Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), and the Department of Health and Human Services (HHS) have published an advisory on the threat of Ryuk ransomware.
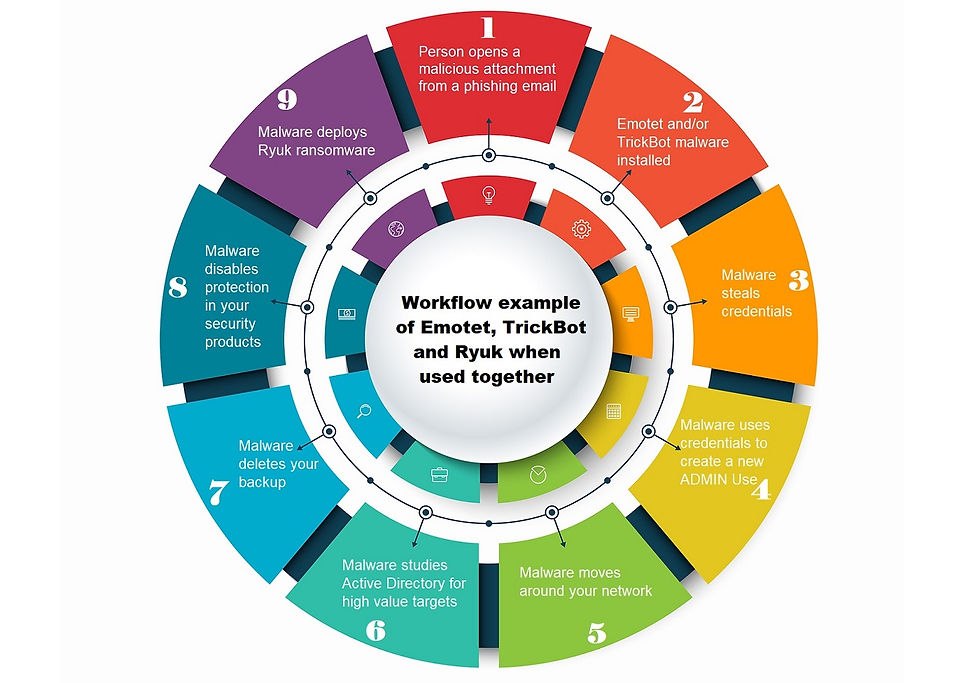
The advisory outlines the tactics, techniques, and procedures (TTPs) used by cyber criminals against U.S. hospitals, wider U.S. healthcare organizations, and the public health sector. It notes that the ransomware in question are Ryuk and Confi, which infect systems with the intent of financial gain. In this case, they are targeting the healthcare sector using the loaders TrickBot and Emotet malware. These insert the ransomware into the network often leading to data theft and the disruption of healthcare services.
All in the healthcare sector, whether public or private, or advised to watch for phishing attempts. Managers are advised to warn users that phishing may end up in their email inboxes regardless of other security tools that are put into place. Spam filters don’t catch everything and the cybercriminals are quite crafty these days and getting better at making email look like it’s legitimate. In fact, this attack reportedly uses messages that actually contain the name of the organization or recipient in the message. However, they also contain malicious documents.
All organizations should get a plan in place to perform regular backups of important data. How often that is depends on the type of industry. For some, maybe weekly is fine, but if losing data or the delay in getting data into the user’s hands may be a matter of life and death, those should occur a lot more often. If backups are completed, restoring the data quickly is a much easier task to accomplish if ransomware does strike.
Because ransomware is evolving and finding where the backup data is held, it is also encrypting those files. Be sure to keep those away from the operational network and completely separate from Internet access.
COVID-19 cases are spiking and hospitalizations are surging across the country. FireEye Inc. said these attacks are being carried out by the group UNC1878. It has seen several U.S hospitals hit by a “coordinated” ransomware attack. It noted that at least three of these have confirmed they were struck the same week and several others were attacked recently.
According to a separate security company, TrickBot has been highly active of late and has attacked more than 400 hospitals in the U.S.
Keep up to date: Sign up for our Fraud alerts and Updates newsletter
Want to schedule a conversation? Please email us at advisor@nadicent.com


Comments